As organizations traverse the intricate web of the internet, the risks associated with fraudulent activities have surged, necessitating robust and innovative fraud detection solutions. This brings us to the main point of our exploration today – Fraud Detection Neo4j Vs Nected.
Neo4j, a powerful graph database management system, works well against fraudulent endeavors through its unique graph-based approach. On the other, Nected asserts its prowess as a rule engine and workflow automation platform, presenting an alternative route to comprehensive fraud prevention. The divergence in their methodologies sets the stage for an insightful comparison, providing businesses with a nuanced understanding of their capabilities.
As you explore the comparative analysis of fraud detection using Neo4j and Nected, it is vital to recognize the rising demand for innovative fraud prevention mechanisms. Join us on this exploration as we dissect the functionalities, strengths, and tangible applications of Neo4j and Nected, navigating the intricate landscape of fraud detection in the digital age.
Understanding Fraud Detection with Neo4j

Embarking on the journey of fraud detection with Neo4j opens up a unique perspective, delving into the world of graph databases. Neo4j provides a powerful tool for uncovering intricate relationships within vast datasets, making it an invaluable asset in efforts to prevent fraud.
Graph Database Advantages

Neo4j's aura DB adept use of the graph database model enables the representation of data as interconnected nodes and relationships. This approach excels in unraveling complex webs of connections between entities, offering a granular understanding of transactional relationships in fraud detection.
Transaction Pattern Recognition Example
Neo4j's capability to recognize intricate transaction patterns is a significant asset in fraud detection. By analyzing the relationships between entities and discerning patterns in their transactions, you can unveil anomalies that might go unnoticed in traditional database systems.
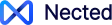
Let us take a scenario where fraudsters attempt to validate stolen credit card information by making small transactions to check if the card is still active.
The scenario is - A fraudster gains access to a list of stolen credit card details. Instead of making large, conspicuous transactions that could trigger alerts, they opt for a more subtle approach.
How is Pattern recognized?
- The fraudster initiates a series of small transactions, often below typical purchase thresholds, to avoid immediate detection.
- Transactions may occur in a sequential manner, testing the card's validity with minimal suspicion.
- The fraudster may perform multiple transactions in rapid succession, aiming to exploit the time lapse between the transactions and the alert system's response time.
- If the card details include location data, the fraudster might test the card across different geographical regions to further avoid detection.
Fraud detection systems, especially those utilizing graph databases like Neo4j, can recognize these patterns by analyzing the relationships between the user accounts, transactions, and the sequential nature of the testing. Unusual transaction patterns, especially those deviating from the user's typical behavior, can trigger alerts for further investigation, allowing timely prevention of fraudulent activities.
Scalability and Performance
One of Neo4j's hallmarks is its scalability and performance, especially in handling large volumes of data. In the context of fraud detection, this translates to efficient processing of vast datasets in real-time. Neo4j ensures the detection and response to potential fraudulent activities in a timely manner.
Implementing Fraud Detection with Neo4j
The fraud detection Neo4j tutorial covers setting up the Neo4j environment and delves into implementing fraud detection algorithms. The tutorial provides practical insights into leveraging Neo4j's capabilities for robust fraud prevention.
Implementing fraud detection with Neo4j involves a structured process to leverage its graph database capabilities effectively.
Here's a concise guide to get you started:
1. Environment Setup:
- Begin by installing and configuring Neo4j on your system. You can download the appropriate version from the official Neo4j website.
- Follow the installation instructions to set up the database environment.
2. Data Import and Modeling:
- Prepare your dataset for import into Neo4j. Ensure the data is formatted appropriately, with nodes representing entities and relationships capturing connections.
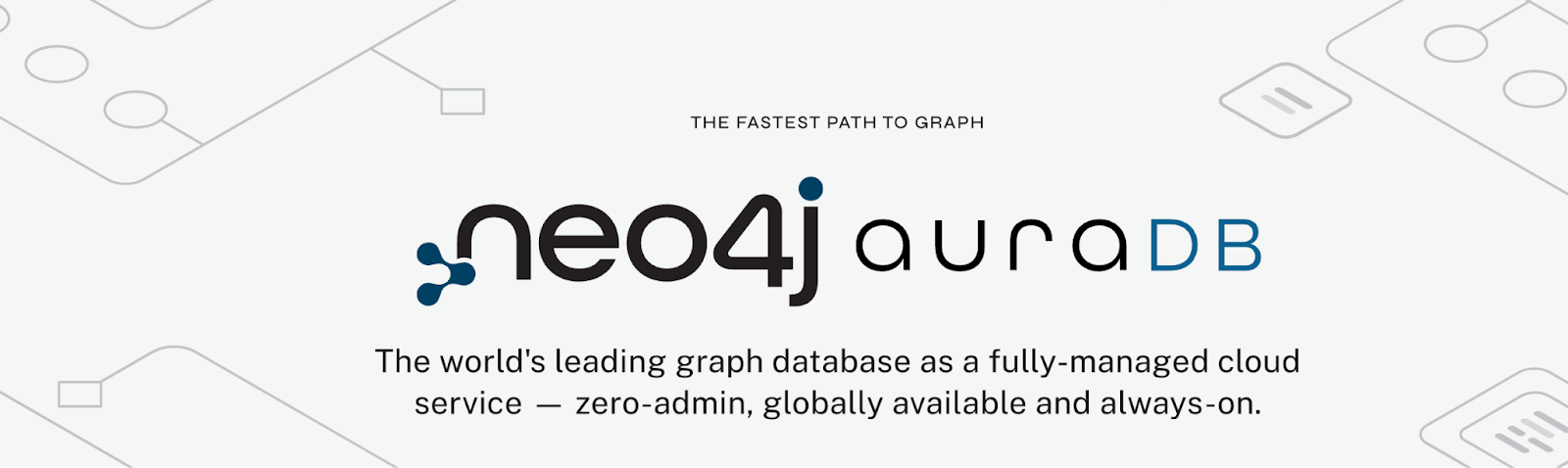
- Use Neo4j's query language, Cypher, to import data and model the relationships within the graph database.
3. Algorithm Selection:
- Neo4j provides various graph algorithms that can be applied to detect patterns indicative of fraud. Common algorithms include community detection, centrality algorithms, and pathfinding algorithms.
- Choose the algorithm that aligns with the specific fraud detection patterns you aim to uncover.
4. Cypher Querying for Fraud Patterns:
- Craft Cypher queries to analyze the graph for potential fraud patterns. Leverage the expressive power of Cypher to traverse relationships and identify anomalies.
- Neo4j's querying capabilities are pivotal in gaining insights into transactional relationships and spotting irregularities.
5. Visualization and Analysis:
- Utilize Neo4j's visualization tools to interpret the results of your fraud detection queries. Visualization provides a clear representation of interconnected nodes and suspicious patterns.
- Analyze the graph to understand the detected fraud indicators and take appropriate preventive measures.
6. Continuous Monitoring and Refinement:
- Implement a monitoring system to continuously assess transactions and patterns within the Neo4j graph database.
- Regularly refine your fraud detection queries and algorithms based on evolving patterns and emerging threats.
This brief overview outlines the key steps in implementing fraud detection with Neo4j. Remember that the effectiveness of your fraud prevention system relies on the careful design of your graph database model and the strategic application of graph algorithms.
Limitations of Neo4j Fraud Detection
While Neo4j offers a robust framework for fraud detection, it's essential to be aware of its limitations.
- Complex Querying Overhead: Neo4j's strength in graph-based modeling can sometimes lead to complex queries, creating overhead in the querying process. Handling intricate relationships may require a deep understanding of Cypher queries.
- Scalability Concerns: Despite its scalability, Neo4j may encounter challenges in handling extremely large datasets. This limitation could impact the system's performance when dealing with an overwhelming volume of transactional data.
- Real-time Performance Bottlenecks: Achieving real-time performance in Neo4j may face bottlenecks, especially when dealing with dynamic and high-velocity data streams. Processing transactions in real-time might pose challenges, impacting the system's responsiveness.
- Learning curve: High Learning Curve is required for working with Neo4j seamlessly as you should be well-versed with Cypher queries understanding, which may not be feasible for especially non-tech users.
Understanding these limitations allows users to make informed decisions about Neo4j's applicability to specific fraud prevention needs.
Exploring Nected's Rules-Based Fraud Detection
Nected employs a sophisticated rules-based approach to fraud detection, providing a robust and customizable solution tailored to your specific needs. Here's an exploration of key aspects in Nected's fraud detection methodology:
1. Customizable Rule Creation:
- Nected empowers you with the ability to create and customize rules according to your unique business requirements. This flexibility ensures that your fraud detection system aligns precisely with your evolving needs.
- The advantage of a rules-based system lies in its adaptability. As fraud patterns change, Nected allows you to swiftly modify rules, providing a dynamic defense against emerging threats.
2. Adaptive Learning and Continuous Improvement:
- Nected's rules engine incorporates adaptive learning mechanisms, enabling it to evolve alongside the changing landscape of fraud tactics. The system learns from historical data, adapting its rules to detect new and sophisticated fraudulent activities.
- Continuous improvement is a core principle of Nected, ensuring that your fraud detection capabilities stay ahead of the curve and provide reliable protection.
3. Ease of Implementation:
- Implementing fraud detection rules in Nected is a straightforward process, designed with user-friendliness in mind. The intuitive interface allows businesses of various sizes and technical backgrounds to seamlessly integrate fraud prevention measures.
- Nected's commitment to simplicity ensures that you can deploy an effective fraud detection system without the need for extensive technical expertise.
Implementing Fraud Detection with Nected
To facilitate a smooth learning process, Nected offers a step-by-step tutorial on implementing fraud detection rules. The tutorial provides practical demonstrations, guiding users through the process of setting up rules and optimizing them for maximum effectiveness.
By following these basic steps, you can harness the full potential of Nected's rules-based fraud detection and tailor it to address your specific business challenges.
In essence, Nected's rules-based methodology offers a powerful and adaptive solution for fraud detection, combining customization, continuous learning, ease of implementation, and practical guidance for users.
How Nected Overcome Neo4j's Limitations
While Neo4j presents a formidable approach to fraud detection, it does have its limitations. Nected steps in to address these challenges, offering a solution that overcomes Neo4j's constraints:
- Enhanced Scalability: Nected provides enhanced scalability, ensuring efficient handling of large volumes of data. This addresses one of the limitations faced by Neo4j in managing real-time fraud detection processes.
- Improved Efficiency in Complex Models: Nected's rules-based approach excels in dealing with complex models, offering resource-efficient solutions where Neo4j might face challenges.
Why Choose Nected Over Neo4j or Other Fraud Detection Tools?
When it comes to selecting the right fraud detection tool, Nected stands out as a superior choice for several compelling reasons:
1. Rule-Based Versatility: Nected's rule-based system offers unparalleled versatility, allowing you to create and customize rules tailored to your unique fraud prevention needs. This adaptability ensures a precise and dynamic defense against evolving fraud patterns.
2. Scalability and Performance: Nected excels in scalability and performance, ensuring that your fraud detection system can handle increasing data volumes without compromising efficiency. This is crucial for real-time fraud detection processes.
3. Cost-Effective Solution: Nected provides a cost-effective solution, offering robust fraud detection capabilities without exorbitant expenses. The affordability of Nected makes it an attractive option for businesses of all sizes.
4. Comprehensive Support and Training: Nected goes beyond providing a tool; it offers comprehensive support and training to ensure that users can harness the full potential of the platform. This commitment to customer success sets Nected apart.
5. Customizability for Unique Business Needs: Tailor Nected to your specific business needs with its high degree of customizability. This ensures that your fraud detection system aligns precisely with your operational requirements.
6. Proven Accuracy and Reliability: Nected boasts proven accuracy and reliability, backed by a track record of effectively detecting fraudulent activities. The platform's performance instills confidence in its users.
7. Integrated Ecosystem: Nected offers an integrated ecosystem that seamlessly integrates with your existing systems, providing a cohesive solution for fraud detection within your business operations.
In conclusion, Nected emerges as a comprehensive and superior choice in fraud detection, offering a versatile, adaptive, and user-friendly solution that addresses the limitations of other tools like Neo4j.
Create Fraud Alerts for your Business today with Nected.
Conclusion
In the dynamic landscape of fraud detection, both Neo4j and Nected bring unique strengths to the table. Neo4j, with its graph database model, offers a robust foundation for uncovering complex relationships within data, while Nected's rules-based approach provides unparalleled adaptability and ease of implementation. As you navigate the choice between these solutions, it's crucial to assess your specific business needs.
Your decision hinges on factors like scalability, customization, and the nature of fraud patterns your business encounters. For those seeking a versatile, rule-based system that evolves with emerging threats, Nected proves to be a compelling choice. On the other hand, if your focus is on leveraging a graph database model, Neo4j might align more closely with your requirements.
The effectiveness of your fraud detection strategy relies on choosing the right tool for the job. Explore both Neo4j and Nected further, delving into their features, implementations, and limitations. By making an informed decision based on your unique circumstances, you position your business for robust and tailored fraud prevention.
Ready to fortify your fraud detection strategy? Explore Nected's adaptive and rule-based approach – a versatile solution designed to evolve with your business. Make the informed choice for lasting protection against fraudulent activities.

FAQ
Q1. Can Nected's rules-based system effectively handle real-time fraud detection?
Absolutely. Nected's rules engine is designed for real-time fraud detection, offering a swift and adaptive response to potential threats. With customizable rules and adaptive learning capabilities, Nected excels in identifying and mitigating fraud in real-time scenarios.
Q2. How does Nected overcome the limitations of Neo4j in fraud detection?
Nected addresses limitations observed in Neo4j by providing a rules-based system that is less dependent on the quality of the dataset. It offers customizable rules, adaptive learning, and continuous improvement, ensuring robust fraud detection even with unstructured or noisy data. Explore Nected's features to understand how it overcomes specific limitations.


.svg)




.png)
.webp)





.svg.webp)










%2520(3).webp)
_result.webp)









%20(1).webp)