Organizations face a constant challenge to strengthen their defenses against evolving cyber threats. For instance, organizations always try to safeguard their data from fraudulent activities using advanced fraud detection and prevention mechanisms.
Fraud prevention means stopping scams before they happen and using advanced tools to detect fraud early. For example, a bank system can spot a weird transaction outside the country, or a firewall can stop someone from accessing a file without permission.
Detection and prevention of Frauds technology addresses and resolves issues related to unauthorized access, financial scams, and other fraudulent activities in an organization. These tools detect anomalies, unusual patterns, and suspicious behavior, allowing organizations to act immediately.
If you want to learn more about the tools and processes of fraud detection and prevention, continue reading this article. The article delves into various aspects, from anomaly detection to behavioral analytics, covering a range of tools that redefine how organizations safeguard their assets, data, and reputation.
What’s the Difference Between Fraud Prevention and Fraud Detection?
Are you looking to know fraud prevention vs detection in an easy manner? This table gives a concise overview of the distinctions between fraud prevention and fraud detection.
|
Aspect |
Fraud Detection |
Fraud Prevention |
|
Approach |
Reactive |
Proactive |
|
Goal |
Identify fraud as it happens |
Halt fraud before it happens |
|
Effectiveness |
Allows immediate action, time for investigation and recovery |
Takes advantage of fraudsters' mistakes |
|
Data Analysis |
Looks for patterns indicating fraud in the data |
Examines all available data on user, device, or transaction |
|
Focus |
Identifying and responding to ongoing fraudulent activity |
Avoiding fraudulent activity |
|
Timing |
During or after the occurrence of fraud |
Prior to occurrence of fraud |
Why is Fraud Detection and Prevention Important for Organizations?
It's not just about money; it's about protecting the organization’s reputation, following laws, keeping customer trust, ensuring smooth operations, and making smart decisions in a fast-changing business world. Fraud detection and prevention are crucial for organizations due to several critical reasons:
- Financial Loss Mitigation: Fraudulent activities, like embezzlement or unauthorized transactions, can cause significant financial harm to organizations. Implementing effective fraud detection and prevention measures is crucial for protecting the organization's financial health.
- Legal and Regulatory Compliance: Industries face strict regulations on data protection, privacy, and financial transactions. Failing to have strong fraud prevention measures can result in legal consequences and regulatory non-compliance, leading to fines and penalties.
- Operational Continuity: Fraud can disrupt normal business operations, causing downtime, loss of productivity, and increased operational costs. Robust fraud prevention measures ensure operational continuity and stability.
- Preventing Insider Threats: Guarding against internal threats, such as fraudulent activities by employees, is crucial. Insider threats are challenging to detect, making proactive prevention measures essential for mitigating these risks.
Tips on How to Prevent fraud
To effectively prevent fraud, your can consider following important tips:
1. Check Unexpected Requests: Always verify the identity of anyone asking for personal information or money. Scammers often impersonate known figures or organizations while interacting. Login requests should also be carefully verified.
2. Secure Payment Methods: Use payment methods that offer fraud protection such as credit cards and OTPs.
3. Regular Accounts Monitoring: Keep an eye on your bank and credit card statements. For regular monitoring, you can weekly check statements for any unauthorized transactions. Report if you find any suspicious activity.
4. Educate Yourself: As the world is changing, fraudsters are scamming people through new tactics. Stay informed about common fraud schemes and aware other people as well. Organize sessions to educate and help your employees and CXOs to recognize potential scams.
Read a detailed blog on Fraud Detection Techniques.
Key Challenges for Successful Fraud Detection and Prevention Policy

Making sure fraud is detected early and prevented is a must for organizations. Addressing the following challenges helps organizations build a robust defense against fraudulent activities:
- Fraudsters are always adapting and evolving their techniques. Staying updated requires investment in advanced technologies and ongoing training for security teams.
- Stringent security measures shouldn't compromise the user experience. Striking a balance between robust security and user-friendly processes is crucial to prevent frustration.
- Gathering and analyzing data for fraud prevention must comply with data protection regulations. Balancing effective fraud detection with privacy laws is a delicate challenge.
- Many fraud incidents require real-time detection and response. Implementing systems for real-time identification poses technological challenges to avoid significant losses.
- Overly aggressive fraud detection systems may generate false positives. Balancing accuracy to avoid unnecessary disruptions is critical for a positive customer experience.
Check this table to understand different types of fraud and the strategies to prevent them.,
Different frauds are taking place in the market, making it challenging for organizations to be safe from exploitation. So, what's the best way to keep your data extremely safe?
To mitigate such issues and stay ahead in maintaining organizational safety towards fraud, you can use an all-in-one fraud detection and prevention tool called Nected.
Later on in this blog, you will get to know in detail about how Nected can help you with fraud detection and prevention.
Limitations of Traditional Methods for Fraud Detection and Prevention
While once effective, traditional fraud detection and prevention methods have certain limitations that may hinder their ability to combat the evolving landscape of fraudulent activities.
Here are some standard traditional methods and their associated limitations:
- Manual Review and Rule-Based Systems: Manual reviews and rule-based systems can be time-consuming and prone to human error. As fraudsters employ more sophisticated tactics, static rule sets may struggle to keep up with emerging patterns.
- Signature-Based Antivirus Software: Signature-based antivirus solutions rely on known patterns of malware. They may fail to detect new and previously unseen threats, making them less effective against zero-day attacks and polymorphic malware.
- Static Passwords: Static passwords are susceptible to breaches through various means, such as phishing, brute-force attacks, and credential stuffing. Once compromised, a static password provides unfettered access.
- High False Positive Rates: Some traditional methods, especially rule-based systems, may generate many false positives, leading to unnecessary disruptions and straining resources as legitimate transactions are flagged as potentially fraudulent.
Most of the traditional methods are inefficient; thus, the need for an alternative solution arises. Organizations are increasingly turning to alternative solutions, such as Nected, in response to these limitations.
Nected is a cloud-based fraud detection solution that offers scalability and flexibility. It enables organizations to leverage the features without needing extensive on-premises infrastructure, ensuring agility in adapting to changing threat landscapes.
The low-code/no-code workflow creator tool can create a systemic fraud prevention and detection mechanism. Using the tool, you can set rules, and when someone tries to gain access to the system, the tool sends you predefined customized alerts, keeping you aware of what has happened in the system.
You can swiftly modify preset rules within minutes, adapting in real-time to meet your specific conditions. For instance, if someone is trying to gain access to your system through identity theft, the system will alert you about any fraud detected if you have enabled nested rules.
How Can You Implement Fraud Detection and Prevention with Nected?
Consider an organization where the manager has administrative access to its IT resources. The admin can log in using an Admin ID and has the authority to manage resources for employees and transfer funds to vendors. The admin uses a tool called Nected to enhance the security and safekeeping of the system.
Nected provides a fraud detection and prevention tool that allows the admin to set specific rules for its usage. For example, by implementing necessary measures, the admin can establish rules to prevent unauthorized access during resource allocation and fund transfers.
Let's understand the whole scenario with a detailed example.
- Login Process: The admin logs into the system using the preset Login Location, Admin ID, and the IP.
- Resource Management: Once logged in, the admin can add, remove, or transfer IT resources to employees.
- Rule Setting: The admin configures Nected to enforce specific security rules, for critical actions or requiring periodic notification alerts.
- Fund Transfers: The admin can transfer funds to vendors securely through the system. Nected monitors fund transfer patterns and immediately alerts the admin or security team if it detects any unusual or unauthorized transactions.
- Fraud Detection: If someone attempts to gain unauthorized access by guessing wrong credentials, Nected's monitoring capabilities make it difficult for them to succeed. Unusual patterns, such as multiple failed login attempts or unexpected fund transfers, trigger alerts for potential fraud.
Now, let’s see how you can use the Nected tool to set up such a complex rule swiftly and effortlessly.
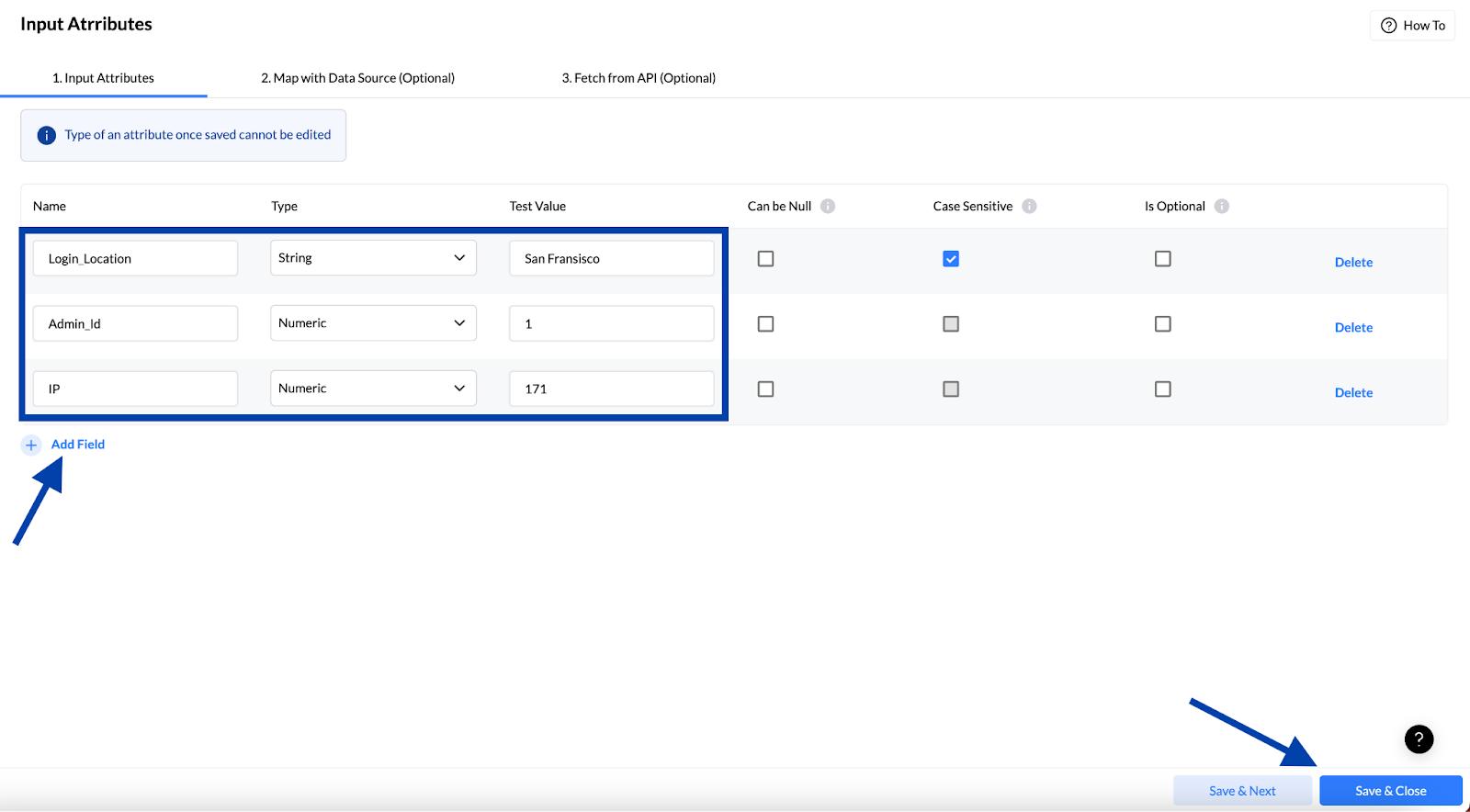
Step 1: App Login
Login to the Nected App.
On the left side, there are numerous options, among which you should click on the "Rules" tab and proceed.
Step 2: Creating A Rule
- Click on the “Create Rule” tab in the top left corner.
- You will get three options: Simple Rule, Decision Table, and Rules Set.
- Select the “Simple Rule” option to start with.
Step 3: Basic Rules Inputs
After clicking on the tab, you will get an interface where you must enter a name for the rule. For instance, in this example, we have used the name "Fraud Detection.
Also, you can set a rule description in the section below. For example, in this instance, we have used the description like:
In this rule, the authoritative access holder, for instance, the administrator, has to input the login details, such as Login Location, Admin ID, the IP address. If the credentials match, they can enter the tool; otherwise, it will show "Fraud Detected."

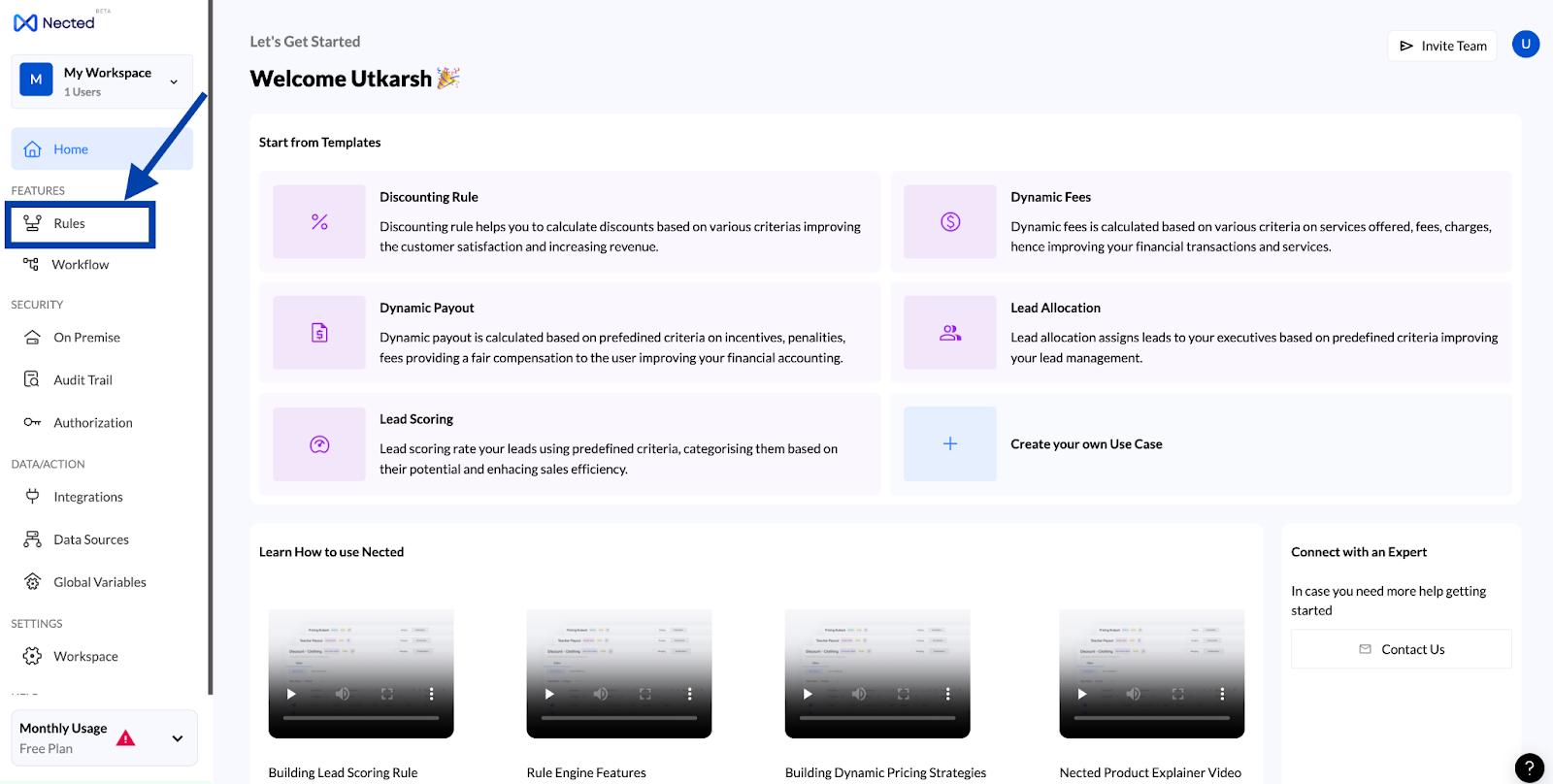
Step 4: Adding Key Attributes
For example, here we are taking 3 attributes.
- Login_Location
- Admin_Id
- IP
You can select different attributes, and there is no limit to the number of attributes. You can assign any number of attributes with your desired values. Click on "Add fields" to add more attributes to the rule.
Step 5: Logic Creation
Here, you must set the logical rules and add the required input data using And/Or logic to set the If-Else statement.
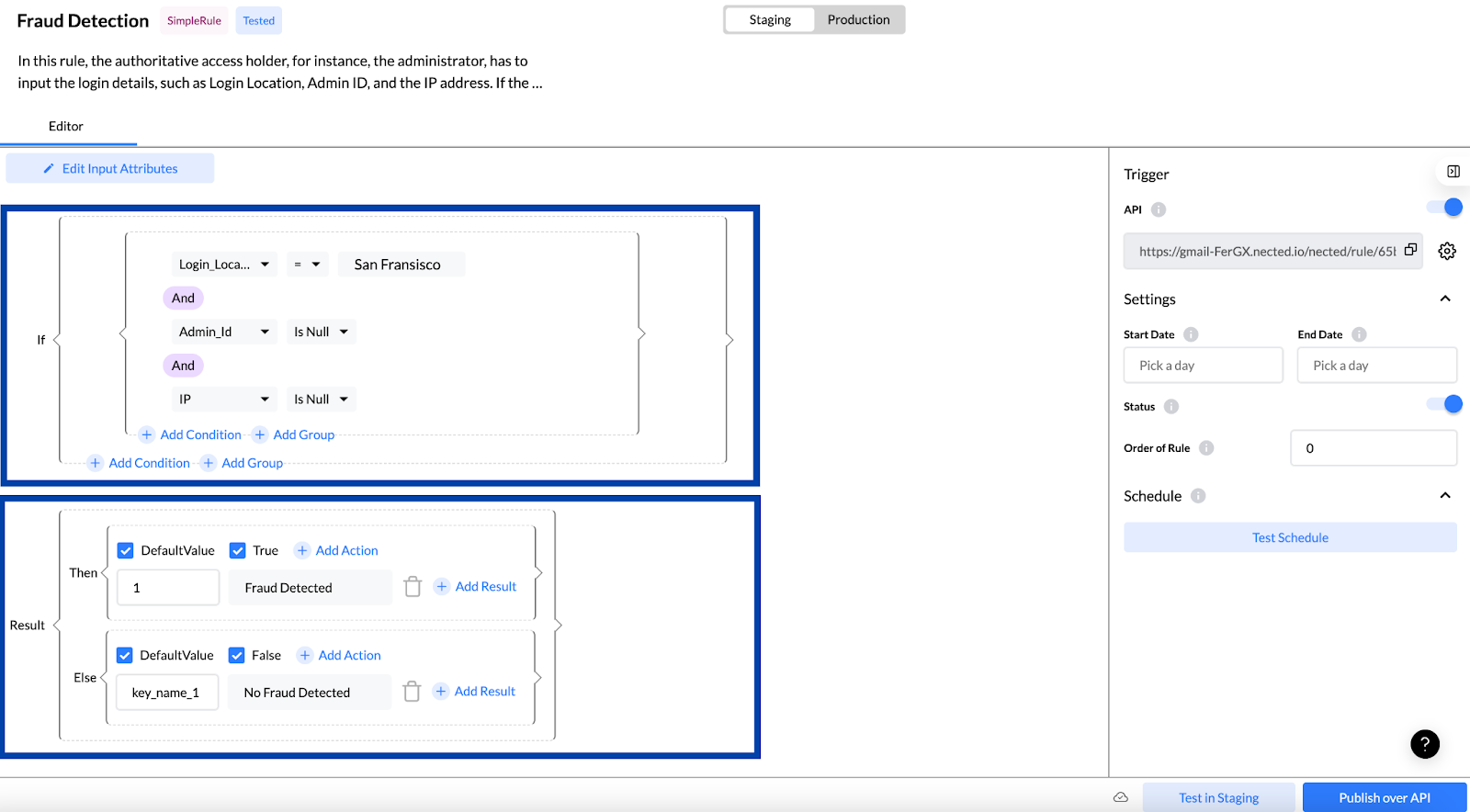
Step 6: Testing The Created New Rule
Now, as your rule is ready, you can click on "Test in Staging" to verify if your rule works.
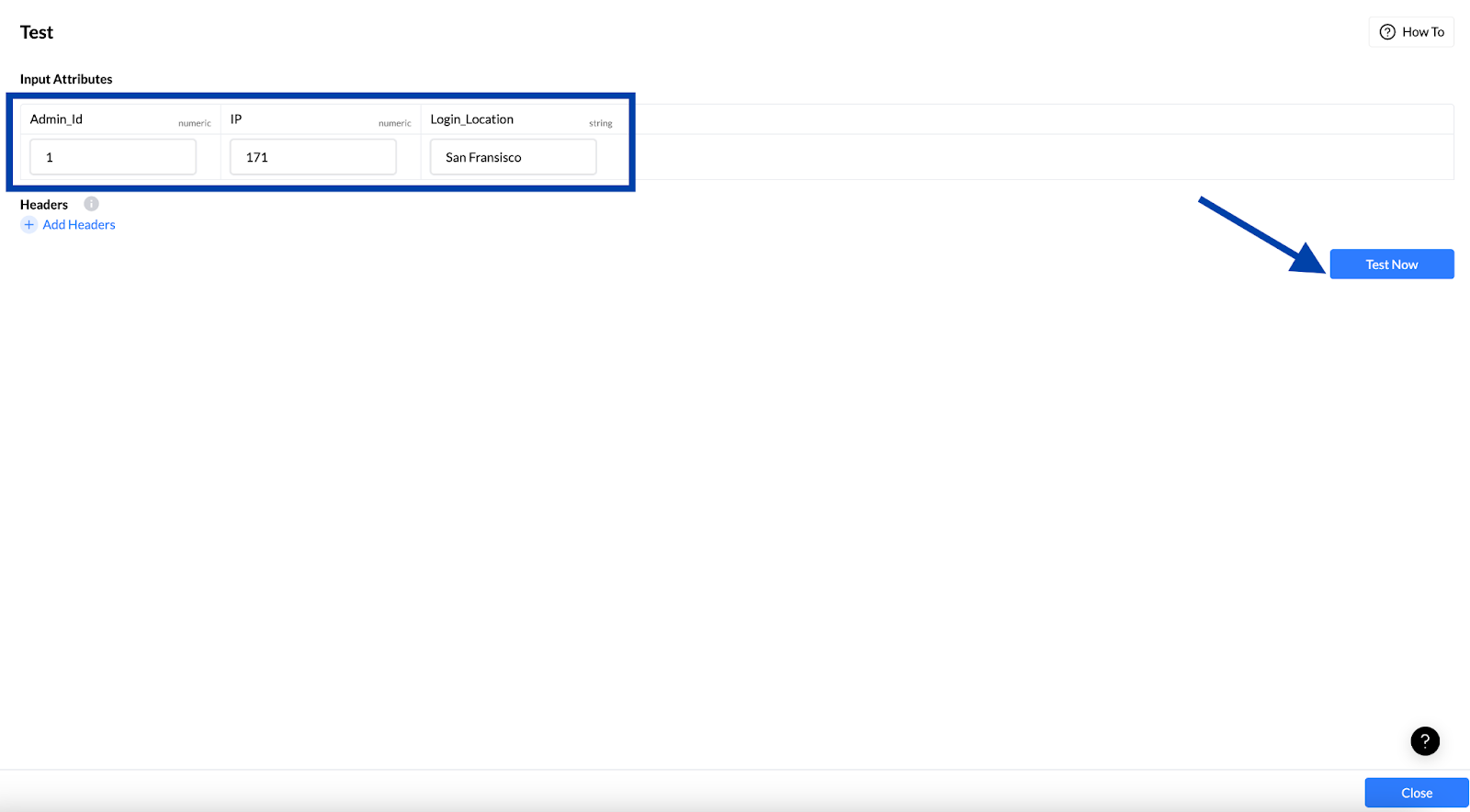
Step 7: Code Execution
Click on “Test Now” and wait for the code to execute.
If you get the green signal with the message that says "Rule tested successfully," your code is working correctly, and you can use it.
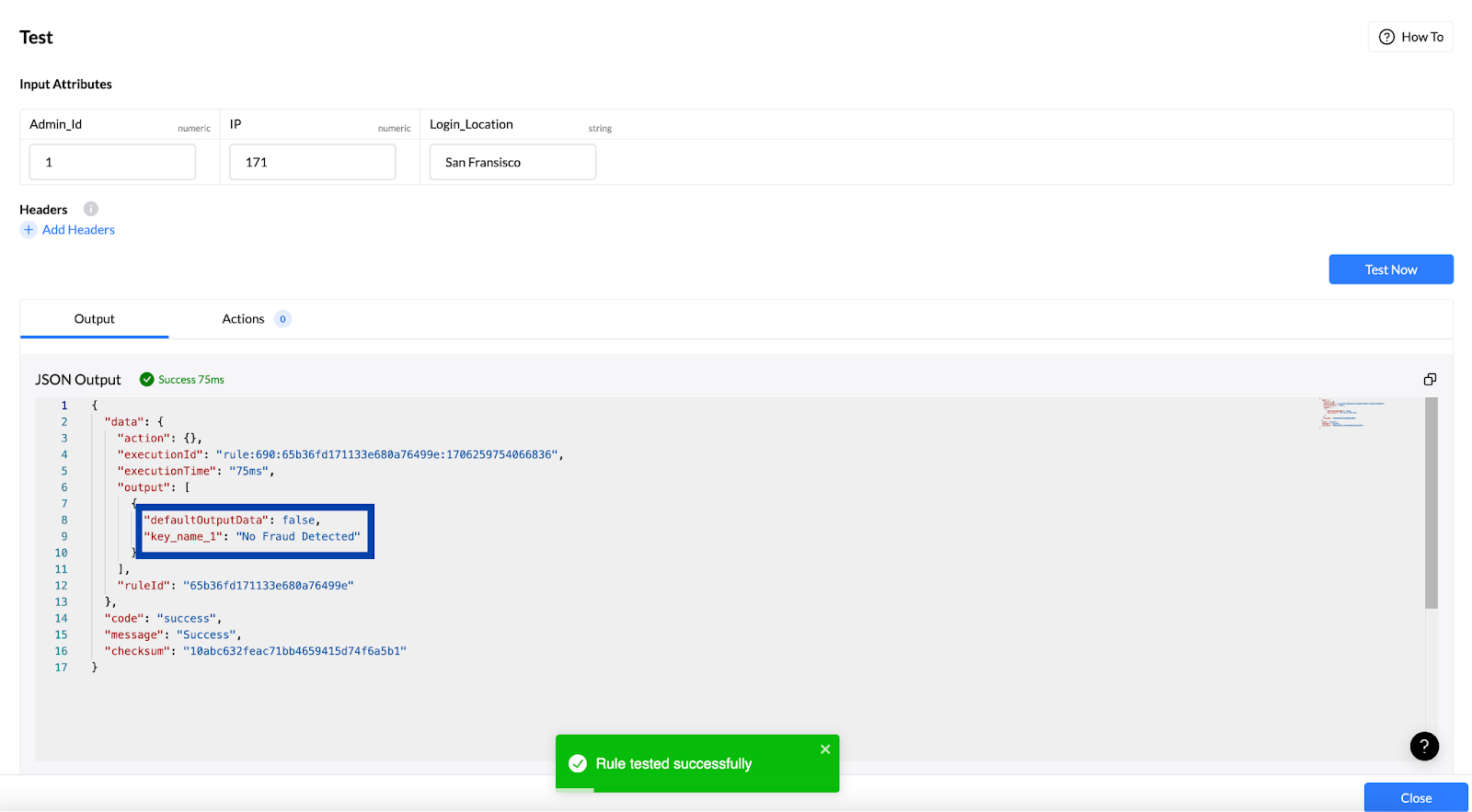
You can publish this over APIs and integrate it into your desired applications or projects.
Sign up now for Nected to enhance your organization's fraud detection and prevention efforts, enabling a robust mechanism.
Key Usability of Nected’s Fraud Detection and Prevention Mechanism
This table will help you with different kinds of fraud detection. This table provides examples of the tools' use cases, their unique features, and their key features.
|
Key Use Case |
Explanation |
What The Tool Does? |
|
Financial Fraud Detection |
Real-time monitoring for financial fraud activities. |
Identity verification in real-time. Fraud case management and reporting. |
|
Account Takeover Detection |
Identifying and preventing unauthorized access. |
Real-time identity verification. Creating Low-code/No-code workflows. |
|
Fake Account Prevention |
Proactive measures against fraudulent account creation. |
Real-time identity verification. Low-code workflows. |
|
Fraudulent Activity Monitoring |
Continuous monitoring for timely fraud detection. |
Real-time identity verificationFraud case management and reporting. |
|
Customizable Fraudulent Activity Detection Alert |
Flexible alerts for suspicious activities. |
Real-time identity verification. Fraud case management and reporting. |
Nected’s unique capabilities make it one of the most reliable tools for organizations focusing on SaaS fraud detection.
Generate fraud alerts quickly using Nected.
Transform Your Organization's Security with Nected’s Fraud Detection and Prevention Analytics Mechanism
To sum it up, fraud detection and prevention techniques are changing. Traditional methods that once worked well now show their limits against smarter and more complex fraud schemes. It has led organizations to seek a more reliable, flexible, efficient, and adaptive approach, turning to advanced tools like Nected.
But this shift isn't just about reacting to fraud when it happens. It's about being proactive and staying one step ahead. Machine learning models generate fraud scores, helping organizations prioritize and respond faster. Deep learning techniques are used for image and video analysis, boosting defenses against identity fraud.
To enjoy the most reliable fraud detection and prevention services provided by Nected, Schedule a demo with the expert team.
FAQs
Q1. How does a rules-based fraud detection system function?
A rules-based fraud detection system utilizes predefined rules and conditions to identify patterns indicative of fraudulent activities. It ensures prompt detection and prevention of fraudulent behavior.
Q2. What sets Nected apart as the preferred choice for rules-based fraud detection?
Nected stands out in rules-based fraud detection by providing an intuitive interface for creating rules, decision tables, and rule sets. With advanced tools and real-time monitoring capabilities, it is a reliable option for efficient and effective fraud prevention.
Q3. What are examples of fraud detection?
Here are the most common types of fraud detections: Credit Card Fraud Detection, Identity theft detection, Payroll Fraud Detection, Insurance fraud Detection, and Investment fraud Detection.
Q4. What is the role of fraud detection?
The role of Fraud detection systems are simple. They use smart algorithms and data analysis to check vast amount of information to identify unusual patterns or behaviors that might signal fraud. By doing so, these fraud detection systems protect a company’s assets, keep consumers data safe, and ensure that businesses operate with integrity.
Q5. How do banks prevent identity fraud?
Banks follow a variety of strategies to prevent payment and identity fraud. They utilize advanced technologies and processes to enhance security and protect customers. For example: Biometric Verification, Artificial Intelligence and Machine Learning, Know Your Customer (KYC) Processes, Document Verification, Limit in Daily Transactions and Two-Factor Authentication (2FA).


.svg)
.svg)




.png)
.webp)





.svg.webp)













.webp)



.webp)
%252520(1).webp)



%20(1).webp)